We have introduced a new Security Threat category called Scam. Relevant domains are marked with the Scam category. Scam typically refers to fraudulent websites and schemes designed to trick victims into giving away money or personal information.
New category added
Parent ID Parent Name Category ID Category Name 21 Security Threats 191 Scam Refer to Gateway domain categories to learn more.
This week’s update spotlights several vulnerabilities across Apache Tomcat, MongoDB, and Fortinet FortiWeb. Several flaws related with a memory leak in Apache Tomcat can lead to a denial-of-service attack. Additionally, a code injection flaw in MongoDB's Mongoose library allows attackers to bypass security controls to access restricted data.
Key Findings
-
Fortinet FortiWeb (CVE-2025-25257): An improper neutralization of special elements used in a SQL command vulnerability in Fortinet FortiWeb versions allows an unauthenticated attacker to execute unauthorized SQL code or commands.
-
Apache Tomcat (CVE-2025-31650): A improper Input Validation vulnerability in Apache Tomcat that could create memory leak when incorrect error handling for some invalid HTTP priority headers resulted in incomplete clean-up of the failed request.
-
MongoDB (CVE-2024-53900, CVE:CVE-2025-23061): Improper use of
$wherein match and a nested$wherefilter with apopulate()match in Mongoose can lead to search injection.
Impact
These vulnerabilities target user-facing components, web application servers, and back-end databases. A SQL injection flaw in Fortinet FortiWeb can lead to data theft or system compromise. A separate issue in Apache Tomcat involves a memory leak from improper input validation, which could be exploited for a denial-of-service (DoS) attack. Finally, a vulnerability in MongoDB's Mongoose library allows attackers to bypass security filters and access unauthorized data through malicious search queries.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100804 BerriAI - SSRF - CVE:CVE-2024-6587 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100812 Fortinet FortiWeb - Remote Code Execution - CVE:CVE-2025-25257 Log Block This is a New Detection Cloudflare Managed Ruleset 100813 Apache Tomcat - DoS - CVE:CVE-2025-31650 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100815 MongoDB - Remote Code Execution - CVE:CVE-2024-53900, CVE:CVE-2025-23061 Log Block This is a New Detection Cloudflare Managed Ruleset 100816 MongoDB - Remote Code Execution - CVE:CVE-2024-53900, CVE:CVE-2025-23061 Log Block This is a New Detection -
A new Beta release for the Windows WARP client is now available on the beta releases downloads page.
This release contains minor fixes and improvements.
Changes and improvements
- Improvements to better manage multi-user pre-login registrations.
- Fixed an issue preventing devices from reaching split-tunneled traffic even when WARP was disconnected.
- Fix to prevent WARP from re-enabling its firewall rules after a user-initiated disconnect.
- Improvement to managed network detection checks for faster switching between managed networks.
Known issues
For Windows 11 24H2 users, Microsoft has confirmed a regression that may lead to performance issues like mouse lag, audio cracking, or other slowdowns. Cloudflare recommends users experiencing these issues upgrade to a minimum Windows 11 24H2 version KB5062553 or higher for resolution.
Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.
Devices with
KB5055523installed may receive a warning aboutWin32/ClickFix.ABAbeing present in the installer. To resolve this false positive, update Microsoft Security Intelligence to version 1.429.19.0 or later.DNS resolution may be broken when the following conditions are all true:
- WARP is in Secure Web Gateway without DNS filtering (tunnel-only) mode.
- A custom DNS server address is configured on the primary network adapter.
- The custom DNS server address on the primary network adapter is changed while WARP is connected.
To work around this issue, reconnect the WARP client by toggling off and back on.
A new Beta release for the macOS WARP client is now available on the beta releases downloads page.
This release contains minor fixes and improvements.
Changes and improvements
- Fixed an issue preventing devices from reaching split-tunneled traffic even when WARP was disconnected.
- Fix to prevent WARP from re-enabling its firewall rules after a user-initiated disconnect.
- Improvement to managed network detection checks for faster switching between managed networks.
Known issues
- macOS Sequoia: Due to changes Apple introduced in macOS 15.0.x, the WARP client may not behave as expected. Cloudflare recommends the use of macOS 15.4 or later.
- Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.
Gateway can now apply HTTP filtering to all proxied HTTP requests, not just traffic on standard HTTP (
80) and HTTPS (443) ports. This means all requests can now be filtered by A/V scanning, file sandboxing, Data Loss Prevention (DLP), and more.You can turn this setting on by going to Settings > Network > Firewall and choosing Inspect on all ports.
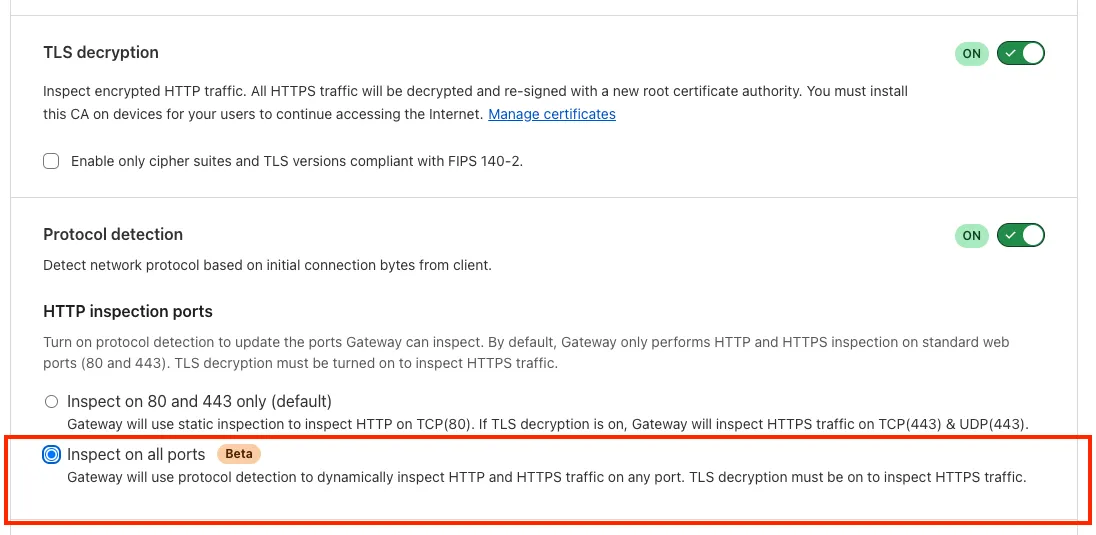
To learn more, refer to Inspect on all ports (Beta).
A new GA release for the Windows WARP client is now available on the stable releases downloads page.
This release contains minor fixes and improvements.
Changes and improvements
- WARP proxy mode now uses the operating system's DNS settings. Changes made to system DNS settings while in proxy mode require the client to be turned off then back on to take effect.
- Changes to the SCCM VPN boundary support feature to no longer restart the SMS Agent Host (
ccmexec.exe) service. - Fixed an issue affecting clients in Split Tunnel Include mode, where access to split-tunneled traffic was blocked after reconnecting the client.
Known issues
For Windows 11 24H2 users, Microsoft has confirmed a regression that may lead to performance issues like mouse lag, audio cracking, or other slowdowns. Cloudflare recommends users experiencing these issues upgrade to a minimum Windows 11 24H2 version KB5062553 or higher for resolution.
Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.
Devices with
KB5055523installed may receive a warning aboutWin32/ClickFix.ABAbeing present in the installer. To resolve this false positive, update Microsoft Security Intelligence to version 1.429.19.0 or later.DNS resolution may be broken when the following conditions are all true:
- WARP is in Secure Web Gateway without DNS filtering (tunnel-only) mode.
- A custom DNS server address is configured on the primary network adapter.
- The custom DNS server address on the primary network adapter is changed while WARP is connected.
To work around this issue, reconnect the WARP client by toggling off and back on.
A new GA release for the macOS WARP client is now available on the stable releases downloads page.
This release contains minor fixes and improvements.
Changes and improvements
- WARP proxy mode now uses the operating system's DNS settings. Changes made to system DNS settings while in proxy mode require the client to be turned off then back on to take effect.
- Fixed an issue affecting clients in Split Tunnel Include mode, where access to split-tunneled traffic was blocked after reconnecting the client.
- For macOS deployments, the WARP client can now be managed using an
mdm.xmlfile placed in/Library/Application Support/Cloudflare/mdm.xml. This new configuration option offers an alternative to the still supported method of deploying a managed plist through an MDM solution.
Known issues
- macOS Sequoia: Due to changes Apple introduced in macOS 15.0.x, the WARP client may not behave as expected. Cloudflare recommends the use of macOS 15.4 or later.
- Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.
A new GA release for the Linux WARP client is now available on the stable releases downloads page.
This release contains minor fixes and improvements.
Changes and improvements
- WARP proxy mode now uses the operating system's DNS settings. Changes made to system DNS settings while in proxy mode require the client to be turned off then back on to take effect.
- Fixed an issue affecting clients in Split Tunnel Include mode, where access to split-tunneled traffic was blocked after reconnecting the client.
Known issues
- Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.
You can now run your Browser Rendering locally using
npx wrangler dev, which spins up a browser directly on your machine before deploying to Cloudflare's global network. By running tests locally, you can quickly develop, debug, and test changes without needing to deploy or worry about usage costs.Get started with this example guide that shows how to use Cloudflare's fork of Puppeteer (you can also use Playwright) to take screenshots of webpages and store the results in Workers KV.
Now, when you connect your Cloudflare Worker to a git repository on GitHub or GitLab, each branch of your repository has its own stable preview URL, that you can use to preview code changes before merging the pull request and deploying to production.
This works the same way that Cloudflare Pages does — every time you create a pull request, you'll automatically get a shareable preview link where you can see your changes running, without affecting production. The link stays the same, even as you add commits to the same branch. These preview URLs are named after your branch and are posted as a comment to each pull request. The URL stays the same with every commit and always points to the latest version of that branch.
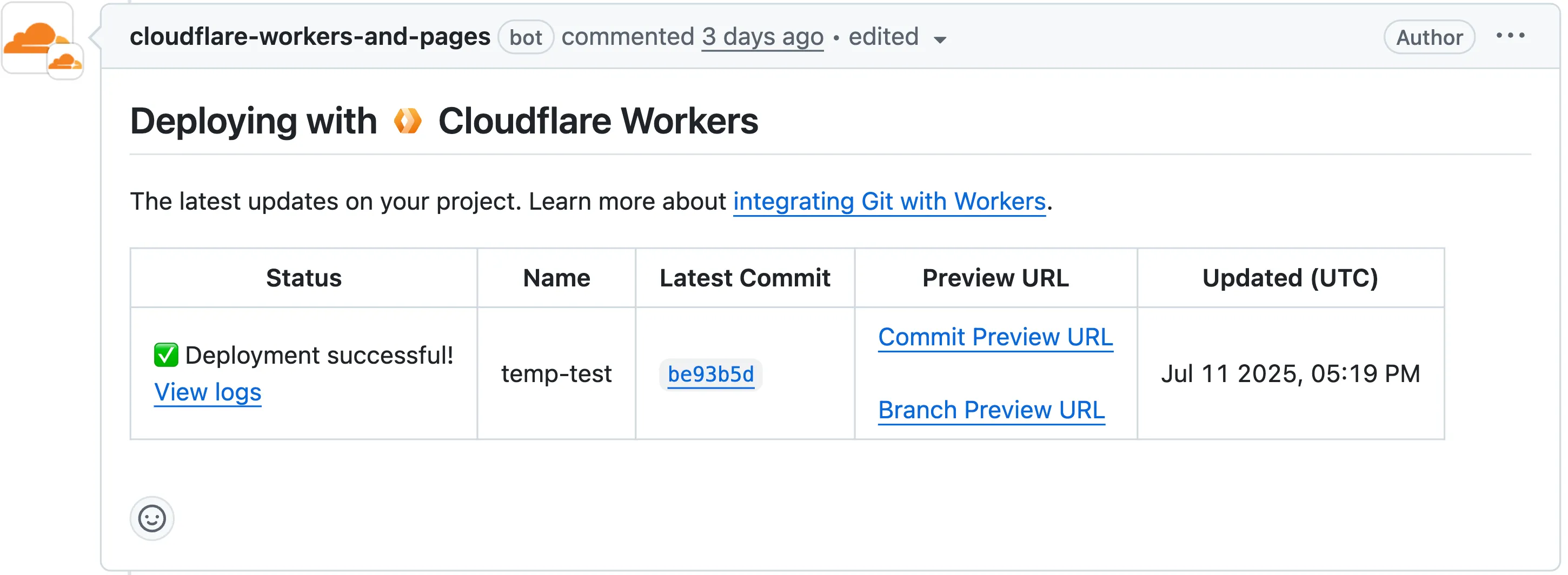
Each comment includes two preview URLs as shown above:
- Commit Preview URL: Unique to the specific version/commit (e.g.,
<version-prefix>-<worker-name>.<subdomain>.workers.dev) - Branch Preview URL: A stable alias based on the branch name (e.g.,
<branch-name>-<worker-name>.<subdomain>.workers.dev)
When you create a pull request:
- A preview alias is automatically created based on the Git branch name (e.g.,
<branch-name>becomes<branch-name>-<worker-name>.<subdomain>.workers.dev) - No configuration is needed, the alias is generated for you
- The link stays the same even as you add commits to the same branch
- Preview URLs are posted directly to your pull request as comments (just like they are in Cloudflare Pages)
You can also assign a custom preview alias using the Wrangler CLI, by passing the
--preview-aliasflag when uploading a version of your Worker:Terminal window wrangler versions upload --preview-alias staging- Only available on the workers.dev subdomain (custom domains not yet supported)
- Requires Wrangler v4.21.0+
- Preview URLs are not generated for Workers that use Durable Objects
- Not yet supported for Workers for Platforms
- Commit Preview URL: Unique to the specific version/commit (e.g.,
The Google Bard application (ID: 1198) has been deprecated and fully removed from the system. It has been replaced by the Gemini application (ID: 1340). Any existing Gateway policies that reference the old Google Bard application will no longer function. To ensure your policies continue to work as intended, you should update them to use the new Gemini application. We recommend replacing all instances of the deprecated Bard application with the new Gemini application in your Gateway policies. For more information about application policies, please see the Cloudflare Gateway documentation.
We now support
audiomode! Use this feature to extract audio from a source video, outputting an M4A file to use in downstream workflows like AI inference, content moderation, or transcription.For example,
Example URL https://example.com/cdn-cgi/media/<OPTIONS>/<SOURCE-VIDEO>https://example.com/cdn-cgi/media/mode=audio,time=3s,duration=60s/<input video with diction>For more information, learn about Transforming Videos.
The KVM-based virtual Cloudflare One Appliance is now in open beta with official support for Proxmox VE.
Customers can deploy the virtual appliance on KVM hypervisors to connect branch or data center networks to Cloudflare WAN without dedicated hardware.
For setup instructions, refer to Configure a virtual Cloudflare One Appliance.
Subaddressing, as defined in RFC 5233 ↗, also known as plus addressing, is now supported in Email Routing. This enables using the "+" separator to augment your custom addresses with arbitrary detail information.
Now you can send an email to
user+detail@example.comand it will be captured by theuser@example.comcustom address. The+detailpart is ignored by Email Routing, but it can be captured next in the processing chain in the logs, an Email Worker or an Agent application ↗.Customers can use this feature to dynamically add context to their emails, such as tracking the source of an email or categorizing emails without needing to create multiple custom addresses.
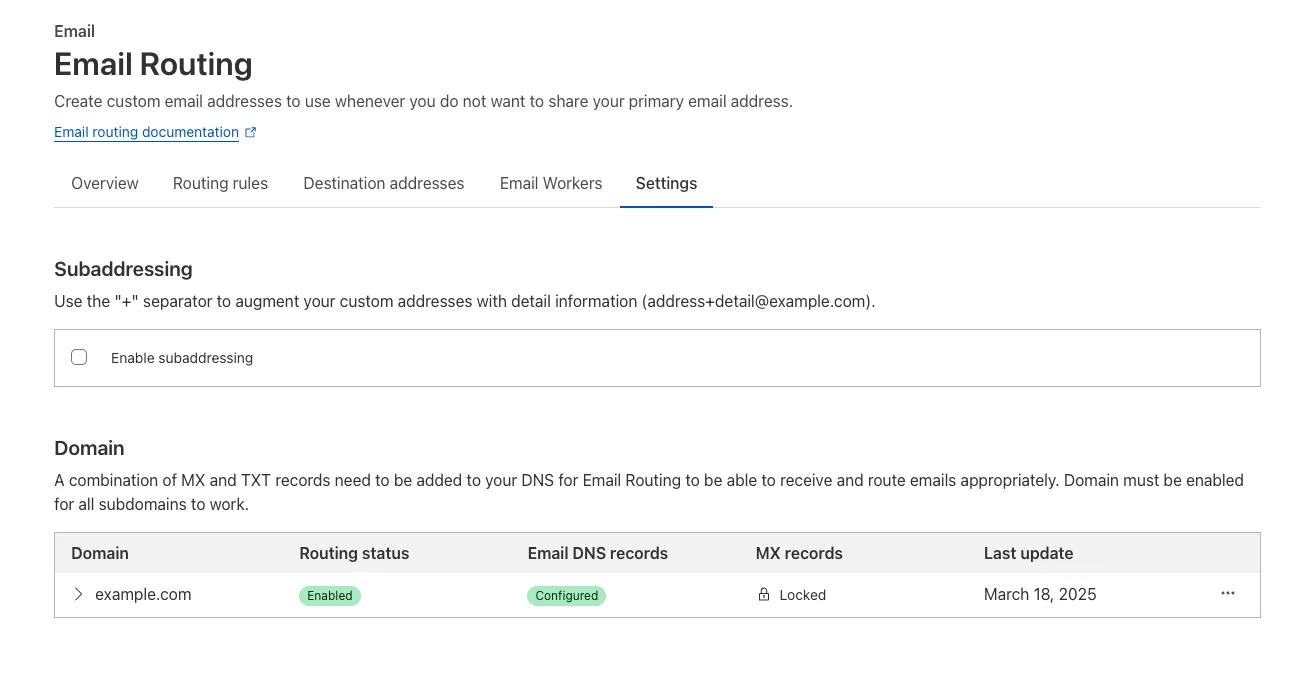
Check our Developer Docs to learn on to enable subaddressing in Email Routing.
This week's update highlights several high-impact vulnerabilities affecting Microsoft SharePoint Server. These flaws, involving unsafe deserialization, allow unauthenticated remote code execution over the network, posing a critical threat to enterprise environments relying on SharePoint for collaboration and document management.
Key Findings
- Microsoft SharePoint Server (CVE-2025-53770): A critical vulnerability involving unsafe deserialization of untrusted data, enabling unauthenticated remote code execution over the network. This flaw allows attackers to execute arbitrary code on vulnerable SharePoint servers without user interaction.
- Microsoft SharePoint Server (CVE-2025-53771): A closely related deserialization issue that can be exploited by unauthenticated attackers, potentially leading to full system compromise. The vulnerability highlights continued risks around insecure serialization logic in enterprise collaboration platforms.
Impact
Together, these vulnerabilities significantly weaken the security posture of on-premise Microsoft SharePoint Server deployments. By enabling remote code execution without authentication, they open the door for attackers to gain persistent access, deploy malware, and move laterally across enterprise environments.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100817 Microsoft SharePoint - Deserialization - CVE:CVE-2025-53770 N/A Block This is a New Detection Cloudflare Managed Ruleset 100818 Microsoft SharePoint - Deserialization - CVE:CVE-2025-53771 N/A Block This is a New Detection For more details, also refer to our blog ↗.
This week's update spotlights several critical vulnerabilities across Citrix NetScaler Memory Disclosure, FTP servers and network application. Several flaws enable unauthenticated remote code execution or sensitive data exposure, posing a significant risk to enterprise security.
Key Findings
- Wing FTP Server (CVE-2025-47812): A critical Remote Code Execution (RCE) vulnerability that enables unauthenticated attackers to execute arbitrary code with root/SYSTEM-level privileges by exploiting a Lua injection flaw.
- Infoblox NetMRI (CVE-2025-32813): A remote unauthenticated command injection flaw that allows an attacker to execute arbitrary commands, potentially leading to unauthorized access.
- Citrix Netscaler ADC (CVE-2025-5777, CVE-2023-4966): A sensitive information disclosure vulnerability, also known as "Citrix Bleed2", that allows the disclosure of memory and subsequent remote access session hijacking.
- Akamai CloudTest (CVE-2025-49493): An XML External Entity (XXE) injection that could lead to read local files on the system by manipulating XML input.
Impact
These vulnerabilities affect critical enterprise infrastructure, from file transfer services and network management appliances to application delivery controllers. The Wing FTP RCE and Infoblox command injection flaws offer direct paths to deep system compromise, while the Citrix "Bleed2" and Akamai XXE vulnerabilities undermine system integrity by enabling session hijacking and sensitive data theft.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100804 BerriAI - SSRF - CVE:CVE-2024-6587 Log Log This is a New Detection Cloudflare Managed Ruleset 100805 Wing FTP Server - Remote Code Execution - CVE:CVE-2025-47812 Log Block This is a New Detection Cloudflare Managed Ruleset 100807 Infoblox NetMRI - Command Injection - CVE:CVE-2025-32813 Log Block This is a New Detection Cloudflare Managed Ruleset 100808 Citrix Netscaler ADC - Buffer Error - CVE:CVE-2025-5777 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100809 Citrix Netscaler ADC - Information Disclosure - CVE:CVE-2023-4966 Log Block This is a New Detection Cloudflare Managed Ruleset 100810 Akamai CloudTest - XXE - CVE:CVE-2025-49493 Log Block This is a New Detection
The Brand Protection API is now available, allowing users to create new queries and delete existing ones, fetch matches and more!
What you can do:
- create new string or logo query
- delete string or logo queries
- download matches for both logo and string queries
- read matches for both logo and string queries
Ready to start? Check out the Brand Protection API in our documentation.
Vite 7 ↗ is now supported in the Cloudflare Vite plugin. See the Vite changelog ↗ for a list of changes.
Note that the minimum Node.js versions supported by Vite 7 are 20.19 and 22.12. We continue to support Vite 6 so you do not need to immediately upgrade.
You can now create document-based detection entries in DLP by uploading example documents. Cloudflare will encrypt your documents and create a unique fingerprint of the file. This fingerprint is then used to identify similar documents or snippets within your organization's traffic and stored files.
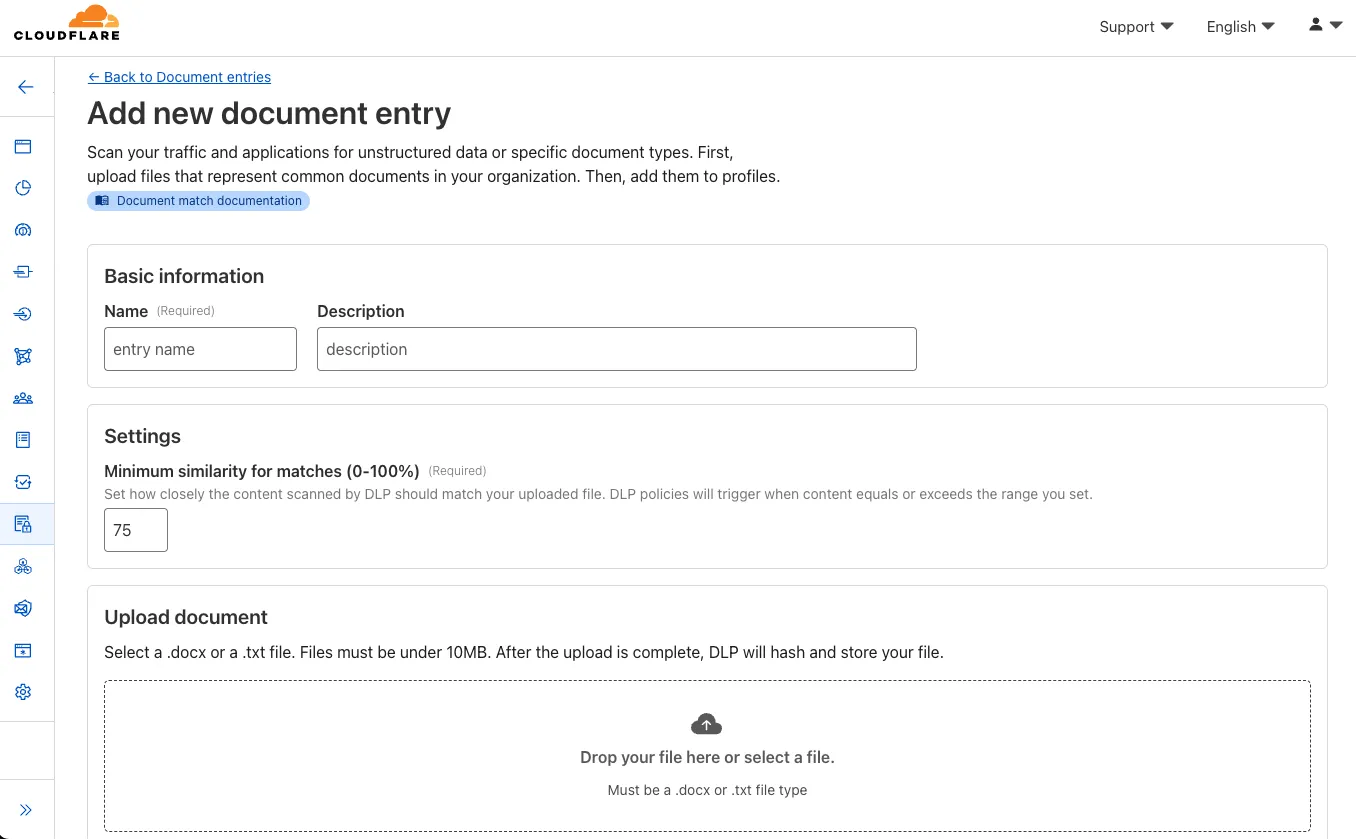
Key features and benefits:
-
Upload documents, forms, or templates: Easily upload .docx and .txt files (up to 10 MB) that contain sensitive information you want to protect.
-
Granular control with similarity percentage: Define a minimum similarity percentage (0-100%) that a document must meet to trigger a detection, reducing false positives.
-
Comprehensive coverage: Apply these document-based detection entries in:
-
Gateway policies: To inspect network traffic for sensitive documents as they are uploaded or shared.
-
CASB (Cloud Access Security Broker): To scan files stored in cloud applications for sensitive documents at rest.
-
-
Identify sensitive data: This new detection entry type is ideal for identifying sensitive data within completed forms, templates, or even small snippets of a larger document, helping you prevent data exfiltration and ensure compliance.
Once uploaded and processed, you can add this new document entry into a DLP profile and policies to enhance your data protection strategy.
-
Your real-time applications running over Cloudflare Tunnel are now faster and more reliable. We've completely re-architected the way
cloudflaredproxies UDP traffic in order to isolate it from other traffic, ensuring latency-sensitive applications like private DNS are no longer slowed down by heavy TCP traffic (like file transfers) on the same Tunnel.This is a foundational improvement to Cloudflare Tunnel, delivered automatically to all customers. There are no settings to configure — your UDP traffic is already flowing faster and more reliably.
What’s new:
- Faster UDP performance: We've significantly reduced the latency for establishing new UDP sessions, making applications like private DNS much more responsive.
- Greater reliability for mixed traffic: UDP packets are no longer affected by heavy TCP traffic, preventing timeouts and connection drops for your real-time services.
Learn more about running TCP or UDP applications and private networks through Cloudflare Tunnel.
Earlier this year, we announced the launch of the new Terraform v5 Provider. We are aware of the high mumber of issues ↗ reported by the Cloudflare community related to the v5 release, with 13.5% of resources impacted. We have committed to releasing improvements on a 2 week cadeance to ensure it's stability and relability, including the v5.7 release.
Thank you for continuing to raise issues and please keep an eye on this changelog for more information about upcoming releases.
- Addressed permanent diff bug on Cloudflare Tunnel config
- State is now saved correctly for Zero Trust Access applications
- Exact match is now working as expected within
data.cloudflare_zero_trust_access_applications cloudflare_zero_trust_access_policynow supports OIDC claims & diff issues resolved- Self hosted applications with private IPs no longer require a public domain for
cloudflare_zero_trust_access_application. - New resource:
cloudflare_zero_trust_tunnel_warp_connector
- Other bug fixes
For a more detailed look at all of the changes, see the changelog ↗ in GitHub.
- #5563: cloudflare_logpull_retention is missing import ↗
- #5608: cloudflare_zero_trust_access_policy in 5.5.0 provider gives error upon apply unexpected new value: .app_count: was cty.NumberIntVal(0), but now cty.NumberIntVal(1) ↗
- #5612: data.cloudflare_zero_trust_access_applications does not exact match ↗
- #5532: cloudflare_zero_trust_access_identity_provider detects changes on every plan ↗
- #5662: cloudflare_zero_trust_access_policy does not support OIDC claims ↗
- #5565: Running Terraform with the cloudflare_zero_trust_access_policy resource results in updates on every apply, even when no changes are made - breaks idempotency ↗
- #5529: cloudflare_zero_trust_access_application: self hosted applications with private ips require public domain ↗
If you have an unaddressed issue with the provider, we encourage you to check the open issues ↗ and open a new one if one does not already exist for what you are experiencing.
We suggest holding on migration to v5 while we work on stablization of the v5 provider. This will ensure Cloudflare can work ahead and avoid any blocking issues.
If you'd like more information on migrating from v4 to v5, please make use of the migration guide ↗. We have provided automated migration scripts using Grit which simplify the transition, although these do not support implementations which use Terraform modules, so customers making use of modules need to migrate manually. Please make use of
terraform planto test your changes before applying, and let us know if you encounter any additional issues by reporting to our GitHub repository ↗.
This week’s vulnerability analysis highlights emerging web application threats that exploit modern JavaScript behavior and SQL parsing ambiguities. Attackers continue to refine techniques such as attribute overloading and obfuscated logic manipulation to evade detection and compromise front-end and back-end systems.
Key Findings
- XSS – Attribute Overloading: A novel cross-site scripting technique where attackers abuse custom or non-standard HTML attributes to smuggle payloads into the DOM. These payloads evade traditional sanitization logic, especially in frameworks that loosely validate attributes or trust unknown tokens.
- XSS – onToggle Event Abuse: Exploits the lesser-used onToggle event (triggered by elements like
<details>) to execute arbitrary JavaScript when users interact with UI elements. This vector is often overlooked by static analyzers and can be embedded in seemingly benign components.
Impact
These vulnerabilities target both user-facing components and back-end databases, introducing potential vectors for credential theft, session hijacking, or full data exfiltration. The XSS variants bypass conventional filters through overlooked HTML behaviors, while the obfuscated SQLi enables attackers to stealthily probe back-end logic, making them especially difficult to detect and block.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100798 XSS - Attribute Overloading Log Block This is a New Detection Cloudflare Managed Ruleset 100799 XSS - OnToggle Log Block This is a New Detection
Use our brand new onboarding experience for Cloudflare Zero Trust. New and returning users can now engage with a Get Started tab with walkthroughs for setting up common use cases end-to-end.
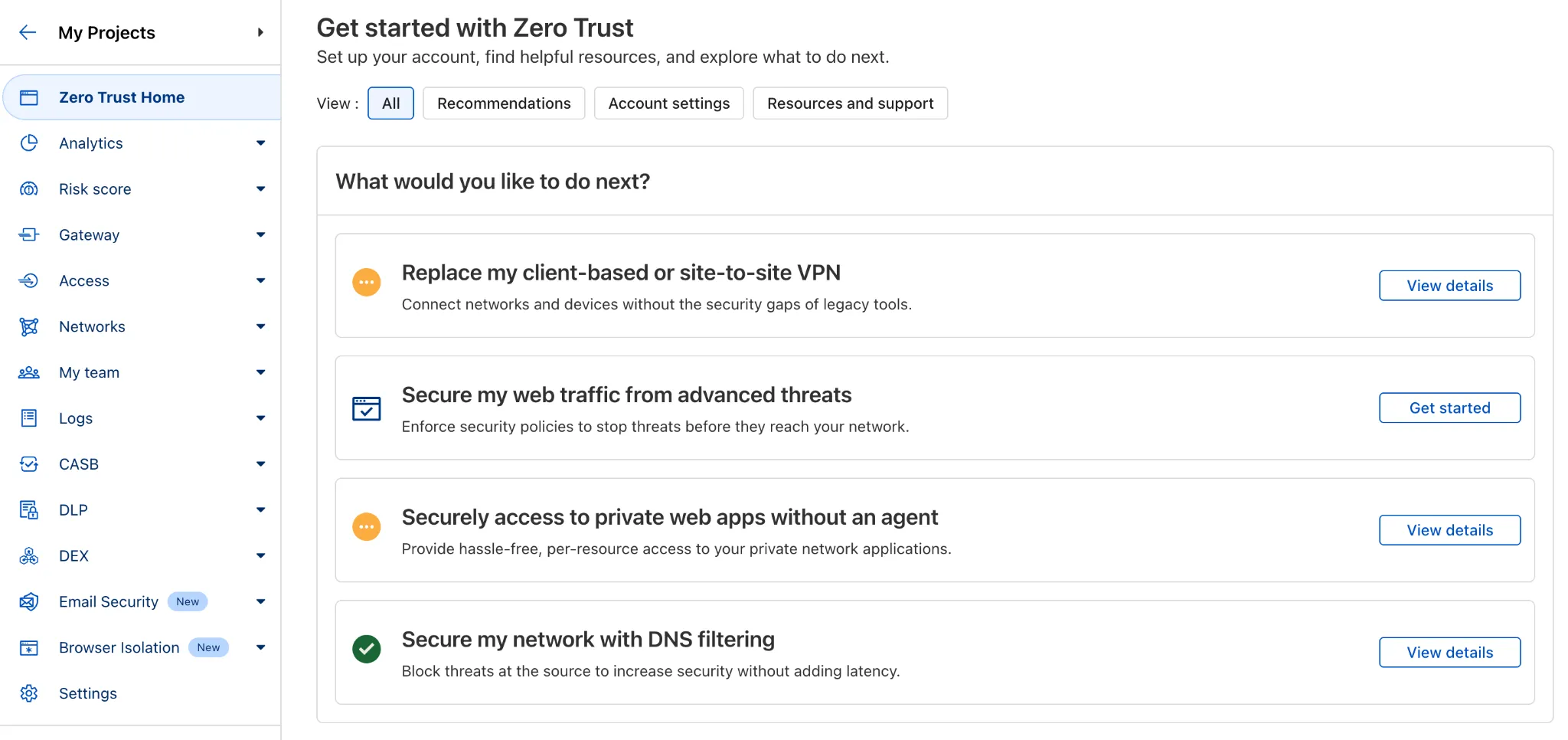
There are eight brand new onboarding guides in total:
- Securely access a private network (sets up device client and Tunnel)
- Device-to-device / mesh networking (sets up and connects multiple device clients)
- Network to network connectivity (sets up and connects multiple WARP Connectors, makes reference to Magic WAN availability for Enterprise)
- Secure web traffic (sets up device client, Gateway, pre-reqs, and initial policies)
- Secure DNS for networks (sets up a new DNS location and Gateway policies)
- Clientless web access (sets up Access to a web app, Tunnel, and public hostname)
- Clientless SSH access (all the same + the web SSH experience)
- Clientless RDP access (all the same + RDP-in-browser)
Each flow walks the user through the steps to configure the essential elements, and provides a “more details” panel with additional contextual information about what the user will accomplish at the end, along with why the steps they take are important.
Try them out now in the Zero Trust dashboard ↗!
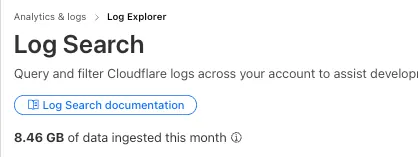
Log Explorer customers can now monitor their data ingestion volume to keep track of their billing. Monthly usage is displayed at the top of the Log Search and Manage Datasets screens in Log Explorer.
You can now expect 3-5× faster indexing in AutoRAG, and with it, a brand new Jobs view to help you monitor indexing progress.
With each AutoRAG, indexing jobs are automatically triggered to sync your data source (i.e. R2 bucket) with your Vectorize index, ensuring new or updated files are reflected in your query results. You can also trigger jobs manually via the Sync API or by clicking “Sync index” in the dashboard.
With the new jobs observability, you can now:
- View the status, job ID, source, start time, duration and last sync time for each indexing job
- Inspect real-time logs of job events (e.g.
Starting indexing data source...) - See a history of past indexing jobs under the Jobs tab of your AutoRAG
This makes it easier to understand what’s happening behind the scenes.
Coming soon: We’re adding APIs to programmatically check indexing status, making it even easier to integrate AutoRAG into your workflows.
Try it out today on the Cloudflare dashboard ↗.